The Qorsa Platform
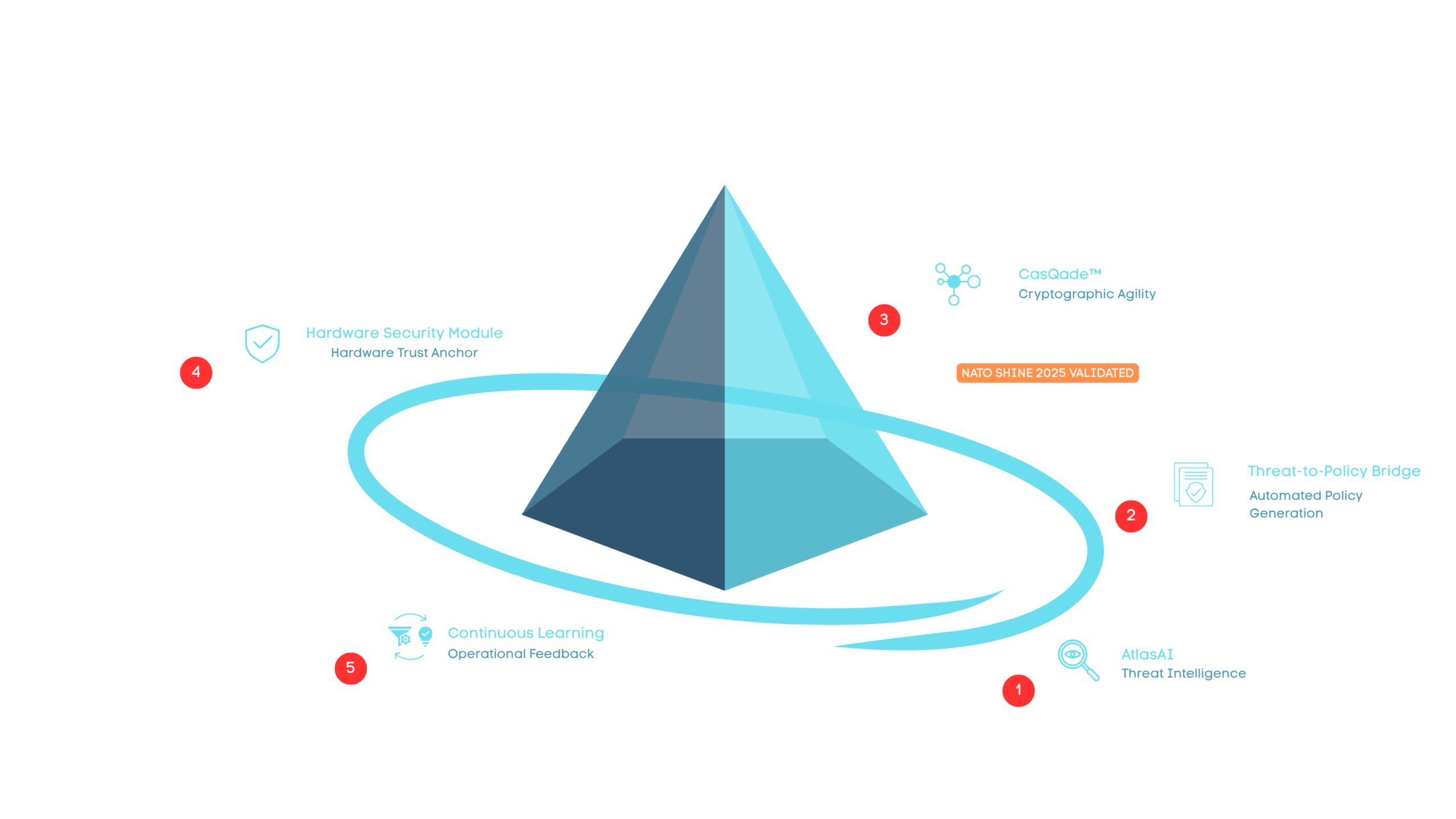
Quantum threats don’t arrive one at a time. They evolve, compound, and exploit the seams between disconnected security tools. Qorsa’s platform is built differently — five capabilities working as a single, integrated defence system that detects, translates, coordinates, executes, and refines protection in seconds across distributed networks.
How It Works
Three pillars. Five Capabilities. Complete Protection.
Why Qorsa
Most security vendors solve one problem well. Qorsa solves the whole problem.
Point Solutions
The Qorsa Platform
Getting Started
Qorsa offers flexible implementation approaches tailored to government and critical infrastructure requirements.
Assess
Evaluation of current cryptographic infrastructure, identification of quantum-vulnerable systems, and roadmap development for quantum readiness.
Pilot
Limited-scope implementations demonstrating capability while building organisational confidence and technical expertise.
Deploy
Comprehensive deployment across government networks, critical infrastructure, or sectoral applications with training and ongoing support.
Proven. Validated. Deployed.
Cryptographic agility validated at NATO SHINE 2025 | Applied research partnership with the University of Waterloo | Headquartered in Waterloo, Ontario, with European operations in The Hague


